Executive Briefing
- The core event: Chinese military UAVs are actively transmitting fraudulent International Civil Aviation Authority (ICAO) transponder codes over the contested South China Sea. Analysts suspect this as Taiwan invasion rehearsal
- The primary data point: At least 23 high-altitude flights have adopted false digital identities since August, impersonating everything from a British fighter jet to a sanctioned Belarusian cargo plane.
- The hidden geopolitical impact: Beyond military misdirection, injecting fake 24-bit addresses into open-source tracking networks actively corrupts the automated data streams that global civilian air traffic controllers rely on to prevent commercial mid-air collisions.

The persistent escalation of Chinese drone spoofing near Taiwan introduces a dangerous new variable into one of the world’s most congested transit corridors. Rather than simply flying without tracking beacons, the People’s Liberation Army is actively broadcasting fraudulent digital identities.
This represents a severe escalation in regional grey-zone warfare.
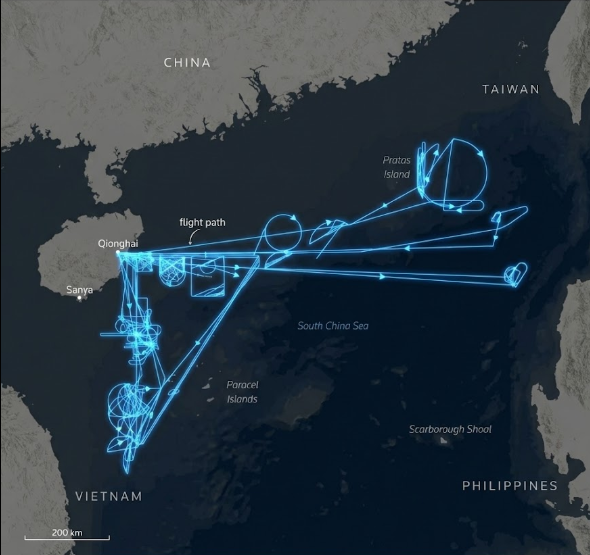
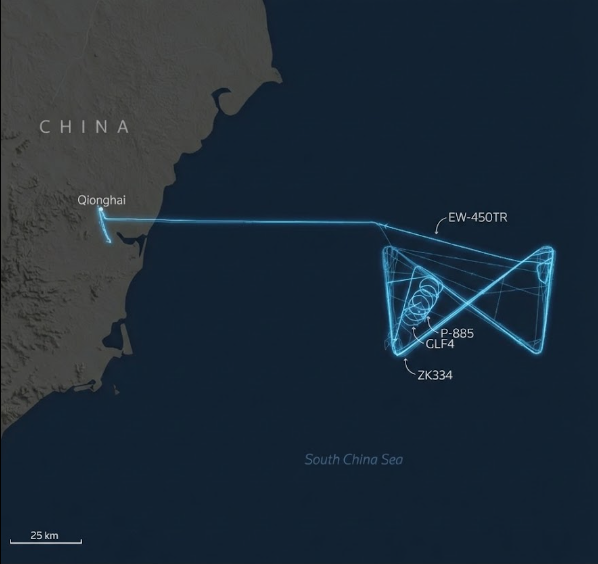
As per Reuters analysis of open-source flight data, a known long-endurance Chinese military drone operating under the call sign YILO4200 has repeatedly masked its true origin. The aircraft launches from the dual-use Qionghai Boao International Airport on Hainan Island.
Once airborne, it manipulates its transponder to project the identity of entirely different aircraft.
The YILO4200 Anomaly and Digital Camouflage
The scale of this deception is highly specific. The flights typically execute prolonged star-shaped or hourglass patterns off the coast of Vietnam and near the Paracel Islands.
During these hours-long missions, the drone’s broadcast data shifts wildly.
On August 5, the drone briefly transmitted a code belonging to a Royal Air Force Typhoon fighter. It then cycled through three other digital identities within twenty minutes. It eventually landed while broadcasting the signal of an Ilyushin-62 cargo plane operated by Rada Airlines—a Belarusian company currently under U.S. sanctions for trafficking Wagner Group personnel.
| Date of Operation | Broadcast Identity | Actual Aircraft Classification | Strategic Purpose |
| August 5, 2025 | RAF Typhoon Fighter | Wing Loong 2 UAV | Testing rapid multi-signal switching in real-time. |
| November 18, 2025 | Rada Airlines Il-62 | Wing Loong 2 UAV | Identity theft while the actual target was airborne near Iran. |
| February 15, 2026 | Pilatus PC-12 | Wing Loong 2 UAV | Blending into regional civilian turboprop traffic. |
Intelligence analysts strongly suspect the aircraft is a Wing Loong 2. This platform heavily resembles the American MQ-9 Reaper. It boasts a 20.5-meter wingspan and is capable of carrying out command operations, precision strikes, and anti-submarine warfare.
Corrupting the Civilian Safety Net
The mainstream consensus views this activity purely as a military rehearsal. Planners assume these operations are dry runs to confuse Taiwanese and American radar operators during a kinetic invasion.
The secondary impact, however, threatens the entire commercial aviation sector.
Global aviation relies heavily on the Automatic Dependent Surveillance-Broadcast (ADS-B) network. Commercial airliners and ground control use these 24-bit addresses to automate collision avoidance systems. When a state actor deliberately injects false data into this open architecture, they weaponize the civilian safety net.
A military drone impersonating a small Pilatus PC-12 passenger plane degrades the trust algorithms of every commercial pilot navigating the South China Sea.
If automated systems cannot verify whether an approaching signal is a civilian turboprop or a massive military drone, the risk of an accidental shoot-down or mid-air collision rises exponentially.
The Bashi Channel Dry Run
The geographic footprint of these flights leaves little room for ambiguity.
The drones frequently push east from Hainan toward the Bashi Channel. This narrow waterway separates Taiwan from the Philippines. It serves as the primary choke point for any Chinese naval fleet attempting to break out into the open Pacific Ocean.
| Strategic Location | Geographic Proximity | Military Value During Conflict |
| Bashi Channel | South of Taiwan | Primary access route for Chinese submarines entering the Pacific. |
| Paracel Islands | East of Vietnam | Forward operating bases and radar early-warning outposts. |
| Okinawa (Ryukyu Chain) | Northeast of Taiwan | Home to massive U.S. and Japanese rapid-response military installations. |
Overlaying these spoofed flight paths onto a map of Taiwan reveals a clear pattern. The drones are tracing the exact trajectories required to monitor Taipei’s defensive installations and southern coastal bases.
In a high-intensity automated conflict, defense systems rely on split-second threat assessments.
Forcing an adversary’s missile defense grid to spend precious milliseconds verifying if an incoming target is a Belarusian cargo plane or an armed Wing Loong 2 provides a massive tactical advantage. Beijing is currently testing exactly how much algorithmic fog it can generate before a shot is ever fired.
Frequently Asked Questions
What is transponder spoofing in military aviation?
Spoofing occurs when an aircraft manipulates its transponder to broadcast a fraudulent 24-bit ICAO address. This makes the aircraft appear on civilian and open-source radar networks as a completely different plane, such as a commercial airliner or an allied fighter jet.
Why are Chinese drones impersonating other aircraft near Taiwan and how is it related to Taiwan invasion rehearsal?
Defense analysts assess these flights as live-action rehearsals for a regional conflict. By rapidly changing digital identities in mid-air, the Chinese military aims to test its ability to sow confusion, delay enemy targeting systems, and mask sensitive surveillance operations across the South China Sea.
ALSO READ: China FTA loopholes 2026: How China Outsmart’s Global Tariffs With The “Made in Anywhere” Strategy
ALSO READ: Cold War 2.0 Is Here , But The Weapons Are Silicon and Sand

Ibrahim is the Founder and Lead Analyst at The Global Angle, an independent digital platform dedicated to factual geopolitical analysis and international affairs. Based in India, he combines an engineering background with a deep focus on global markets, diplomacy, and strategic security. Ibrahim leverages a data-driven, analytical approach to break down complex international conflicts and economic shifts, helping readers see beyond standard news narratives. When he isn’t researching global policy, he focuses on digital publishing, search engine optimization, and platform architecture.